Tag Archives for " Ag & Construction "
Recon SpraySense™ Receives AE50 Award from ASABE

We’re excited to announce that the Intelligent Ag™ solution, Recon SpraySense™ has received an AE50 award for 2023 from the American Society of Agriculture and Biological Engineers (ASABE). This recognition is awarded annually by a diverse panel of engineering experts from around the world.
We are thrilled that Intelligent Ag™ and Recon SpraySense™ were named among 50 of the best innovations in engineering and technology for agriculture, food, and biological systems in the country.
View the full list of award recipients here.
https://appareo.com/2023/01/11/spraysense-receives-ae50-award/
Artificial Intelligence Provides Great Opportunity for Off-Highway Equipment Industry
David Batcheller of Appareo recently sat down with OEM Off-Highway editor about the potential for Artificial Intelligence (AI) and augmented reality, as well as what challenges and opportunities lie ahead for the heavy equipment industries.
“AI has the potential to make decisions for operators,” says Batcheller. In the off-highway industry, using that capability can help to reduce the amount of training required for operators. Less experienced and well-trained operators can become more effective and more quickly become experts which can help to overcome the current labor shortages construction and other off-highway applications are facing.
You can read the article and watch the full video here: https://www.oemoffhighway.com/trends/video/21723061/ai-provides-great-opportunity-for-offhighway-equipment-industry
https://appareo.com/2021/10/27/artificial-intelligence-provides-great-opportunity-for-off-highway-equipment-industry/
Why Your Supplier Should Help You Write that RFP
Innovating is hard. Providing guidance to highly technical suppliers to create innovation for your vehicles is even harder — but it doesn’t have to be. If you have strong supply chain relationships, your suppliers should be part of the solution in bringing your ideas to the market. To do so, however, requires a slightly different approach.
Why not to start with the RFI/RFP
Don’t come to your key suppliers leading with a Request for Information (RFI) or Request for Proposal (RFP). To do that, one first must independently research a great deal in the technology space in which your supplier is (or should be) an expert. That research takes time and money, which delays your ability to approach the market with your solution to the problem.
Oftentimes, looking into the available literature in any technology space also ignores where the space is going. This hurts you two ways. This first is that it leads to responses from suppliers based on yesterday’s technology, instead of tomorrow’s. The second is that your highest value suppliers will be slowed down further in their response, working through your initial RFI and then crafting a combination of corrections to the technology requests as well as suggestions for how to better craft a later procurement stage for tomorrow’s technology, instead of yesterday’s.
How to leverage suppliers to create RFIs and RFPs
Ask your suppliers to help you with a business problem. This means approaching a highly technical supplier not with the specific piece of technology you want to source, but instead with a problem statement about the end user’s problem that you’re intending to solve with technology.
For example:
- If your business is frustrated with the expense associated with service technicians applying in-warranty software updates, ask your supplier for technology solutions to solve that problem.
- Too often we see highly specific RFIs prescribing a hardware and software solution to this problem that is more complex and expensive than is necessary
- If your business is facing market pressure from a competitor who recently launched new and exciting technology, ask your supplier for advice on how to both match and extend beyond your competitor’s innovation.
- Unfortunately, we frequently see RFIs that match new competitors’ offerings. This results in a business being stuck behind a competitor, who is continually moving onward, as businesses work to innovate only in a manner that “catches up.” In our experience, there are always affordable, noteworthy, opportunities to be different.
- If your business is challenged achieving cost reduction or efficiency targets and trying to figure out how to consolidate electronics or functions to achieve those targets, ask your supplier for advice on how to achieve maximum consolidative benefit for minimal complexity, cost, and risk.
- One “gotcha” we see here is the consolidation of components with different evolutionary rates, leading to accelerated obsolescence pressure on technologies that could be highly resistant to technology-based obsolescence.
Building habits for supplier-delivered success
Great suppliers love these conversations and understand that delivering value for their customers is accomplished by fostering these kinds of conversations — even when the conversation may not deliver new production income for their business. Structuring the conversation in a manner that doesn’t bias your supplier to a specific approach, and providing the freedom for their team to creatively encounter your business problem with a different lens, will bring great results.
Make it a habit to do this a couple of times a year. Choose a few key suppliers and provide business-level problems to them, asking them to bring their unique technology lens and focus to your business problem.
Guarantee you’ll love the results.

David Batcheller
President & CBO https://appareo.com/2021/04/05/why-your-supplier-should-help-you-write-that-rfp/
Critical Questions to Ask a Potential New Electronics Supplier
Manufacturers are faced with many different technologies to be considered in the design, manufacture, and deployment of new vehicles. In many circumstances, it isn’t practical for one manufacturer’s engineering group to really understand how to best leverage these technologies to create differentiation that positively separates your brand from the competition. Separation from your competition is important, and that makes the selection of the right supply chain partner an important task.
So how do you evaluate suppliers to find out if they have the right “stuff” to deliver on the differentiation you need? In this post we will outline what you should consider when selecting the right partner.
Demonstrated Capability
Find a supplier you’re excited about and ask about the last time they helped transform a customer’s business through their technology. Even if the technology is not what you are interested in right now, it’s critical to know if they have experience fielding new technological developments, even if in an adjacent industry. Being first to the world with an technology approach to a problem is hard, and you want to work with people who have been down that road before and understand how difficult it is likely to be. Then, you can be more confident they have the will to overcome the unknown obstacles that will come along the way.
Where we’ve seen some of these partnerships break apart in the past is when organizations who have never really moved an industry attempt something audacious, not understanding how difficult it is really going to be. You have to make sure you’ve got a supplier that is going to step up when the going gets tough, because it will.
Make sure that your supplier can explain new and exciting technologies both in a layperson sense and in a highly technical manner. As Einstein once said, if you can’t explain something simply, you don’t understand it. Don’t let acronyms, jargon, and engineering talk convince you of a supplier’s competency. Make sure they can explain the technology in a way the board, your engineers, and your end customer would understand and are convinced by.
Philosophy & Culture
Innovation is hard. To create technology-based differentiation, with the intent of winning market share, innovating with your supplier is going to hurt a little bit. Doing innovation of real marketplace consequence is challenging — it will take longer, cost more, and challenge your business and your supply chain partnership in ways that cannot be anticipated at the outset. That means you need to have a strong alignment and shared philosophy with your supplier at the outset, to make sure your partnership can weather the storm.
So what do you evaluate in the initial conversations with this new supplier to find out if that alignment is really there?
We’re big advocates of bringing business problems to technical supply chain partners on a regular basis, to challenge them to open new, high-value, differentiable opportunities for your business. If you’re being introduced to a new potential supplier and looking to see if you have a fit, ask them about:
1. The most difficult part of a significant development from their business. Ask specifically about the biggest surprise — the real challenge they never saw coming.
- A great potential partner is going to be honest and describe something that really, really sucked. They’re going to use it as an opportunity to highlight their team’s heroics and how they overcame the challenge. Beware of suppliers who cannot be real about facing a challenge. If they’ve never seen it, they’re the wrong people, and if they can’t be honest about it, how are they going to be transparent with you when it becomes really hard during your project?
2. Where they see a specific technology going in the next five years in your industry. Challenge them to defend the opinion.
- You want a supplier that is convicted about your approach and shares your strong opinion about where you are headed. Difficult things take a shared commitment; asking your supplier to defend a shared opinion early, and utilize some devil’s advocacy to test that convocation, is a great way to explore this early.
3. Something that everyone in the industry generally believes to be true about emerging technology that they completely disagree with.
- Great new innovations come with some controversy. The incumbents that are disrupted by the innovation will defend the conventional approach. Test your partner by asking where they disagree with the conventional approach and challenge them to defend it.
Testing Commercial Alignment
Talk early about the investment that both businesses are going to make in fielding a new and exciting solution for the market. There is both a real cost and opportunity cost to each new partnership. You should explore why it is a great fit for both of you, at a high level, and feel comfortable that your supplier’s conviction about that fit is real.
It is critical that the potential relationship and return for both you and your supplier are highly aligned, and testing this early is critical for any highly innovative product launch. When the product is going to be risky and innovative, the deployment will sap a lot of mindshare from your supplier — you want to be sure the reward and opportunity for your supplier is going to hold their attention and motivate the level of effort necessary to overcome any timeline, technology, or cost obstacles.

David Batcheller
President & CBO https://appareo.com/2021/03/29/critical-questions-to-ask-a-potential-new-electronics-supplier/
Does your supplier own your data, or do you?
The world is getting more and more connected. I’m connected to my car, my kid’s watch, and my doorbell. If I were to buy a new tractor, loader, or trencher, I’d expect to be connected to that too.
For equipment manufacturers considering their connected strategy, there are two approaches. We’re going to talk a bit about each of those approaches, in general I’m an advocate of the Open approach which is described below.
Open and Closed Approaches
At a really high level, there are two approaches to making equipment connectivity happen. Closed and Open.
The Closed approach is an approach where a supplier brings a full system and solution for connectivity. This includes the onboard telematic unit, the backend/cloud service, and the mobile/web experience. This is attractive because it is an easy button, one stop shop, for connecting a machine. The downside is that you are no longer in control of your data, your customer’s data, and you’re going to rely on the permissions granted by a supplier for information that is increasingly critical to your business. They say data is the new oil, you’ve given your supplier your mineral rights.
The Open approach is an approach where a supplier brings an open system for a telematic controller or asset tracker. This means that you can change the software on the system (either internally or with contract resources). This typically means that you need to develop your own backend/cloud service and mobile/web experience. Undoubtedly, this is harder and requires more effort than a turn-key supplier-delivered approach. As they say, nothing worthwhile is ever easy and we’ll discuss the upside below, but the key is that you control your data, how it is used, and can direct the path of value added services that are built off this data. This data, this digital oil, is incredibly valuable in so many ways.
Control of Data
Before discussing data and value propositions, it is important to understand that to achieve these value propositions you must control the data. There are different perspectives on data ownership. Some people believe that the operator should control the data. Others contend that the ownership of the data should reside with the equipment manufacturers. In any event, your supplier should not own or control your data. It is simply too valuable to have to ask for permission to access, to modify, and to mine.
Decreased Costs
Access to this data provides opportunities for the reduction in costs or avoidance of expenses. These cost reductions come in a number of different packages. Having data about the fleet and its operation can lead to value added services that improve fleet safety, which limits litigation and settlement expenses with a reduction in incidents and accidents. This data can also be used to provide the evidence necessary to negotiate with insurance carriers, providing critical information necessary to manage this growing industry expense. Lastly, the data can be used to understand the circumstances related to warranty claims which can lead to the avoidance of payment on unjust claims and the improvement of design to eliminate future claims in related areas.
Increased Revenue
Control over the data creates potential for delivery of value-added services to customers, which creates potential for new streams of revenue. Such services can include things like web-based analytics that allow for more productive utilization of fleet assets and leveraging data to efficiently schedule and use expected machine downtime for maintenance. Interesting opportunities can also emerge in the monetization of third-party, value-added, services through APIs that allow selective access to your data. In these cases, a programmatic interface is created to allow additional companies to access data, at the customer’s request, to provide more niche services at high value. The access to that data can be monetized, with a fee charged to the third party, giving you a portion of their revenue stream without any of the development or maintenance burden of the niche application.
Expansion Potential
Whenever one of our customers really starts to dig into their data, two things emerge. The first is value. The second is more questions that, if answered, are expected to uncover additional exciting business value.
This is where an open platform is also critical. Answering those questions can involve changes to the software on the telematic unit, changes to the backend architecture to mine/compare/contrast data in different ways, or changes to the mobile experience to better present customer features or track customer behaviors. In this way, the cycle of data acquisition, analysis, and value creation becomes an evergreen – but only if you have the control necessary to drive the evolution of your connected ecosystem. This only happens in an open platform.
Flexibility
We believe you should have the freedom to choose. You should be free to choose which telematic supplier you select for different equipment platforms. You should be free to choose which mobile devices are compatible with your solution. In an open system, you are free to specify, implement, and manage these choices. A constraint of a closed system is that you’re locked into the offerings, and mobile device support, from a single supplier. That supplier may be great, but then you’re also locked into the timelines associated with which that supplier supports new generations of connectivity technology (4G, 5G, etc) as well as the timeliness which with that supplier can offer you access to connectivity services in new countries.
Control of Security
Open doesn’t mean unsecure. Open means having the freedom to impose your cyber rules and requirements on the system, ensuring that your security preferences are embodied in your connected solution. When you own your security you have the comfort of certainty. When you’re working in a closed party system, there are always questions about the security and control of access to your equipment, your data, and your customer’s data.

David Batcheller
President & CBOhttps://appareo.com/2021/03/23/does-your-supplier-own-your-data-or-do-you-2/
Maximizing Battery Life In Portable Electronics: What You Need To Know
Now more than ever, the management of battery capacity is a key factor in delivering a positive or negative experience with portable electronic devices, and ultimately the value your customers derive from them. Running out of battery power and losing access to a battery-powered device can result in a range of frustration — from significant inconvenience to full-blown destruction of key business value. In this blog post, we’re going to talk about essential considerations for how battery life is managed in portable electronic devices.
Over the years, Appareo has worked with many different battery chemistries — from alkaline batteries (e.g. “AA” or “AAA” batteries) that we use in common household devices such as remotes and toys, to specialized chemistries like lithium thionyl chloride for extreme environments. Our focus in this blog post is going to be on lithium-ion polymer batteries, the common battery chemistry used for rechargeable cells.
How Electronics Consumers Can Improve Total Battery Life
Tip 1: Keep a battery well charged and charge it between uses, even if (especially if) you didn’t use most of the battery.
The first reason batteries age and hold less charge is due to the number of cycles. What constitutes a “cycle?” There’s no consensus in the battery community, but in general, a cycle is the function of taking a charged battery, consuming some of its energy, and then replacing that energy by recharging the battery. When less of the battery is consumed, it’s less stress on the battery. Therefore, it’s better for you to recharge a battery after consuming a little bit, as compared to draining the battery completely before recharging.
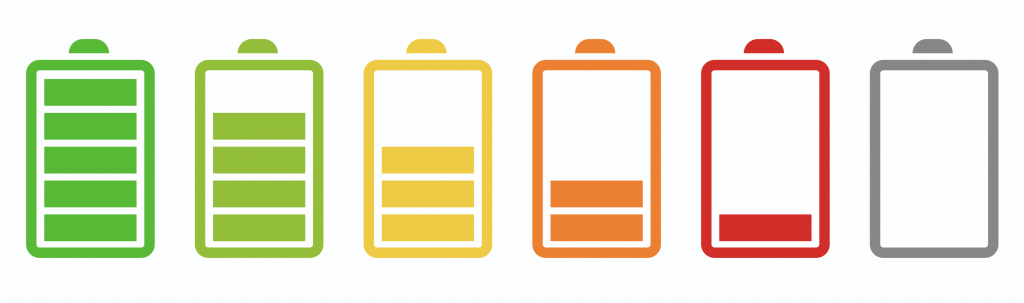
Tip 2: Keep your battery out of hot environments, especially when being stored for longer periods of time.
Another reason batteries permanently lose capacity is due to heat stress. If a battery is exposed to high temps (hotter than 86°F) for extended periods of time, the battery will permanently lose charge. This commonly happens with portable electronic devices that are left in hot cars for hours or days at a time, where high temperatures will stress the battery and destroy its potential.
How Manufacturers Can Improve Total Battery Life
There are reasons that battery life may be diminished that aren’t in the control of the consumer, but instead have to do with the way electronics are specified and implemented. When design engineering a portable electronic device, manufacturers should consider how long customers expect the battery to last, and how much time customers expect to be able to use the device on a charge. One of the ways manufacturers can affect battery performance is by controlling the capacity the battery is operated at. Controlling the capacity involves picking a range that creates the longest battery life, and only operating the battery in that range (e.g. between 25% and 85%). Most batteries will have a longer life in this charge condition than if the battery is operated persistently between 50% and 100% capacity, for example.
A second way manufacturers can have control in this area involves managing the voltage at which the battery is charged. Lowering the charging voltage prevents the battery from getting fully recharged. For example, most batteries are charged at 4.2V. If the charge voltage is lowered to 4.0V, customers may only be able to charge the battery to about 75% of its rated capacity, leaving 25% of the potential battery life on the table. Doing this will increase the number of cycles the battery can withstand by a factor of 2-3 (e.g. from 500 to 1,500 cycles).
Either one, or both, of these approaches will sacrifice total capacity of the battery to improve the life of the battery, and in some applications may be worth the tradeoff.
 Christopher Horne – Director, Electrical and Electronics Design
Christopher Horne – Director, Electrical and Electronics Design
https://www.appareo.com/2021/02/08/maximizing-battery-life-in-portable-electronics-what-you-need-to-know/
Appareo Releases New Open Platform Telematics Device with Truly Global Connectivity
NEWS RELEASE
Appareo Releases New Open Platform Telematics Device with Truly Global Connectivity
The IP67-rated Gateway 370 features Iridium® SBD, 4G/3G/2G, and eSIM, certified for use in the USA, Canada, Europe, Brazil, and more.
FARGO, North Dakota (January 21, 2021) — Appareo today released a new product in the company’s award-winning line of telematic control units (TCUs). The Gateway 370 is a rugged yet lightweight edge computing platform for mobile equipment applications that provides a wide range of communication technologies. This release builds on the Gateway 270 model that was launched in 2020, adding an Iridium short burst data (SBD) satellite transceiver for truly global communication capabilities, and a 433 MHz receiver for use with sensors and active RFID tags.
Gateway 370 is built on an open and flexible platform that supports standard programming languages and tools, allowing Appareo customers to quickly and easily develop their own applications on the hardware. The device is built on a popular distribution of embedded Linux (Yocto) with Docker support, allowing a convenient development environment for C++, C#, or other common development languages.
“This flexibility and approachability gives Appareo customers the control they desire — allowing them to use a variety of approaches and resources to achieve the maintenance, service, and operational benefits customized to their needs,” said David Batcheller, President & CBO of Appareo.
In addition to the satellite and 433 MHz radios, the Gateway 370 comes with the full set of features found in the Gateway 270 model, including global LTE CAT 4 cellular radio with 3G/2G fallback and eSIM; dual core processor for handling significant computational capabilities at the edge; Wi-Fi and Bluetooth interfaces for communication between mobile devices and the machine for control and/or monitoring purposes; 6x CAN bus interfaces; Ethernet; BroadR-Reach; RS-232; GPS; and more.
These capabilities are housed in an IP67-rated rugged enclosure for use outdoors and for mounting on construction and agricultural machinery. The device’s array of wired and wireless communication technologies make it well suited for a broad spectrum of equipment control, monitoring, and connectivity challenges.
Wide Area Network
The Gateway 370 is certified for deployment in a broad range of North American, South American, and European markets, making it ideal for equipment manufacturers with broad geographic distribution. Appareo worked with carrier partners Vodafone International and Tata Communications to maximize the geographic potential of the Gateway 370. However, cellular coverage is still limited in some geographies. Appareo’s inclusion of an Iridium transceiver in Gateway 370 ensures that Appareo customers stay connected with their machines and that critical machine data can be retrieved, wherever that equipment may be (land, air, or water).
Local Area Network
The LAN connections (Wi-Fi, Bluetooth, and 433 MHz) allow machines to communicate directly with each other and with the operators or passengers. For example, people near the machine can be connected, informed, or in control, using real-time data with zero latency and no network costs. Further, the Gateway 370 can communicate with active RFID products (e.g., asset trackers), tire pressure sensors, and other wireless machine sensors. This capability allows for machines to receive information from hydraulic and mechanical attachments, and despite the lack of electrical power on those attachments, use information from the active RFID tag to recognize the attachment, and automatically adjust machine control settings accordingly.
For applications where Iridium is not required and the application may be more cost sensitive, defeatured variants of the Gateway telematic control units are available with the same open platform principle. This family design approach allows Appareo customers to access and utilize a variety of TCUs, on the same open platform, with a variety of capabilities and price points to address specific needs.
Appareo Gateway Series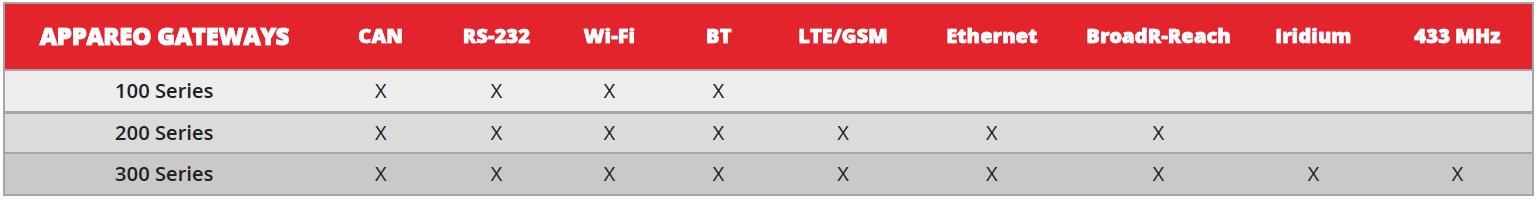
To contact Appareo, acquire a development kit, and begin working with Appareo Gateways, visit appareo.com/gateways.
# # #
About Appareo
Appareo is a recognized leader in the custom design, development and manufacture of innovative electronic and software solutions for aerospace and terrestrial applications. Through the creative application of cutting-edge technologies, Appareo creates complex end-to-end solutions that include both mobile and cloud-based components. The company is privately held, with headquarters in Fargo, N.D., and a design office in Paris, France. All products are built and supported in the USA.
Product Photos: appareo.com/media
https://www.appareo.com/2021/01/21/appareo-releases-new-open-platform-telematics-device-with-truly-global-connectivity/
Configuring Wake Modes to Maximize Battery Life in Cellular Asset Trackers
Operators want to use their expensive machines (loaders, sprayers, excavators, aircraft, etc.) as much as possible, because at the end of the day, business assets are more of an asset when they’re put to work. When a fleet is distributed over a large area, knowing where equipment is so it can be put to work can be a challenge.
Over the last decade, it has become common for larger or more expensive equipment to be delivered from the original equipment manufacturer (OEM) with a telematics standard. Sometimes it’s a simple position reporting modem, other times there’s a huge volume of operating detail being delivered to the cloud. In any event, it makes it much easier for operators to start tracking a fleet of assets when the equipment comes standard with tracking capability.
The challenge
There are still holes when trying to conduct an efficient operation with a full picture of the fleet. These holes exist because many fleets have equipment that did not come with factory telematics.
For example:
- Tenders, dump trucks, and other Milk Run equipment that create the maximum productivity of a working asset also typically do not have stock telematics
- Specialized equipment produced in lower volumes by smaller OEMs, and therefore not factory-equipped with tracking features
- Towed equipment that is not electrified (e.g. trailers, carts, screens, mowers, balers, tedders, rakes, grinders, chippers, etc.) and as a result have no built-in tracking connectivity
- Expensive attachments that are unpowered
- Older equipment that is in good working order but was delivered before connectivity was standard among major OEMs
Considering these holes, you may only be able to track a portion of the fleet. Even if it’s 75%, it’s not good enough. A project can’t happen if only 75% of the equipment is at the site. That makes these holes important to fill, but it also has to be easy. Operators don’t have the time or the interest to assemble a pile of dissimilar aftermarket technology offerings into a fleet tracking solution — they have a business to run.
The good news
In a previous blog (Understanding 4G LTE Categories) we discussed new kinds of cellular technology that have emerged as a portion of 4G offerings. These technologies, specifically NB-IoT and M1, create opportunities for very rugged and affordable “slap and track” cellular asset trackers. These kinds of trackers can be attached to any piece of equipment, and by using their own battery they can report its location for years.
![]()
This can be an easy fix to the problem, but getting real satisfaction out of these solutions is all about managing the battery life of the unit. Why?
- Many rugged asset trackers are made without replaceable batteries in order to achieve an IP67 or IP69K rating. Although these trackers are cheap, they need to be discarded when the battery is used up.
- Trackers with replaceable batteries lose the “easy fix” appeal once you’re spending time tracking down machines to charge their units or replace batteries. The appeal of this solution is ruined if you can’t leave a machine alone for at least a season — ideally for the life of the machine.
So, how do you use “slap and track” solutions to the maximum benefit of your business? I know people hate this answer, but it depends. As you consider your equipment tracking goals, it’s important to understand battery life and wake modes.
Understanding battery life in cellular asset trackers
Battery life is fixed, meaning you start with a bucket of energy and that is all you get. Therefore, to achieve maximum customer value, the focus needs to be about extending the duration of time that a rugged asset tracker can be used.
To maximize that energy:
- Devices need to be off as much as possible
- When on, devices should sparingly use the components that use a lot of energy (e.g. cellular and GPS)
Device manufacturers have put a bunch of battery management tools into these devices, and the asset tracking ecosystem, to make tracking as easy as possible. It varies by manufacturer, but when a device is advertised to have a 5-year lifetime, that’s typically based on an expectation of a few thousand positional reports over its lifetime. That works out to 1-2 position reports per day for five years. So, while the device’s lifetime is marketed in the form of years, in reality the lifetime is based on the number of positional reports utilized.
Understanding how different wake mode configurations affect battery life
Making the most of the battery management tools should get careful consideration as you deploy trackers. We recommend consulting with your tracking services or hardware supplier to dial this in as early as possible. Devices can typically be configured to report in the following ways (organized from most power hungry to least power hungry):
Periodic continuous reporting
For trackers that are integrated into the machine and connected to vehicle power, this is an easy and inexpensive thing to do. However, most customers with battery powered trackers will not want to use this mode. Having the device report every minute, or even every hour, will consume a lot of battery life.
Wake and report on movement
Many asset tracking devices include an accelerometer. These are great because they use minimal energy and can be used to wake the device when it moves. This is helpful if you want to know when equipment is moving from site to site or when equipment has begun working, for example. Depending on the tracker’s capabilities, it might be possible to set the device to report on movement but then to “snooze” for a period of time (e.g. 4 hours). A word of caution, however: if you can’t snooze its reporting behavior, this feature could run through the battery life quickly.
Wake and report on rest
This is related to the movement feature, but it notices when the device stops moving for a period of time (typically configurable) and then reports the device position. It’s an inverted version of the previous feature with the same benefits and challenges.
Start of day / end of day position reporting
This feature is generally easy to configure, easy to implement, and very friendly for battery life. Simply pick a time of day and have the unit report its position at that time every day. This can give you an overview as to where the equipment was left at the end of the day, giving you an opportunity to dispatch resources effectively at the start of the following workday. When combined cleverly with some of the above features (e.g. report equipment position at 5:00 PM, then report on movement in the event someone moves it after hours), it can be used to give an effective and timely overview of fleet positions while using minimal battery.
Wake on demand
This easy to use feature is very powerful and enabled by the newest generation of cellular technologies. For those of you who want to push your glasses a bit higher on your nose and nerd out with us about how this feature works, we’ll dig deeper in a future blog. For this post, we’ll talk about the capability at a high level so you can understand how to exploit it.
Using a computer or mobile device, you ask the equipment to report its location. This feature sends a message over the cellular network, which is stored in a mailbox of sorts. The device periodically checks that mailbox, using very limited energy, to see if it needs to report in. If there’s a request waiting, it reports its location.
The beauty of this feature is that whenever you need to know the location of an asset, you can have the device report in at the push of a button. The report doesn’t come back in seconds, because typically the device is configured to “check the mailbox” at scheduled intervals in order to minimize energy use. However, even waiting a few minutes to get the devices’ location is MUCH faster than driving from site to site looking for it.
Do you want future connectivity advice, insights, and information delivered to your door? Join our email list, and follow us on LinkedIn.
![]() David Batcheller – President & CBO
David Batcheller – President & CBO
https://www.appareo.com/2020/12/14/configuring-wake-modes-to-maximize-battery-life-in-cellular-asset-trackers/
Top two security issues for connected machines
It is important for our machines to be connected. From industrial asset trackers for inexpensive off-road vehicles to satellite telemetry solutions for business jets, original equipment manufacturers (OEMs) are counting on embedded connectivity solutions to deliver high business value for them and their operators. To deliver this value, these connectivity devices are networked to critical onboard engine, hydraulic, display, and navigation equipment to provide the rich data needed to exploit the business value of the connected tractor, loader, or aircraft.
With all of these interconnections and access to critical machine or aircraft systems, there is an obvious need to ensure that such connections are secure. Security is a confusing and acronym-laden space that can leave buyers uncomfortable or uncertain. To combat this, we’ll focus in on the top two areas that you should have a strategy for:
1. The hardware and software on the device itself
2. Transportation of data from device to cloud
Understanding Keys
First, it’s important to understand the concept of a “key” when discussing security concepts for telematic devices. In a simple sense, information is scrambled using an algorithm, and the key unlocks that information. If you’ve ever used paper cutouts over a page of text or a pinwheel decoder to extract a secret message, you’ve experienced a sort of encryption, or cipher, and a key. There are many different manifestations of encryption and key structure, but the concept of an algorithmic encryption and key to enter/exit that encryption are consistent across these concepts.

In a simple sense you can divide security concerns within a telematic device into hardware and software. You need to be confident that the software on the device is genuine, has not been corrupted by some bad actor, and is not attempting to do anything nefarious. You also need to be sure that the hardware is secure, so the electronics are protecting the data resident on the device (including the secret decoder keys that unlock the encryption the device uses to communicate).
Hardware Security Onboard a Device
There are some spectacular tools available to device manufactures to secure applications and storage onboard telematic controllers. For example, Arm TrustZone allows the device manufacturer to secure certain ranges of memory and flash from snooping and sniffing. This security extends to the ability to secure these ranges from the application software onboard the device itself, so even the application running on the device cannot read that data off the flash and send said data to the cloud.
Why is this important? One example of a security vulnerability is to send a false application update to a device, whose express purpose is not to successfully corrupt/replace the application software, but instead is the first component of a multi-stage attack in which the initial attack’s objective is to steal the encryption keys from the device. In such a situation, the application is falsely deployed to the device and retrieves the keys. Even though it fails to update, the device uses the telematic capability of the device to offboard the keys and enable a subsequent, more dangerous attack. With such hardware security enabled, you would not be able to read the protected memory locations, the false application update would be rejected, and the device would continue on its way.
One example of a security vulnerability is to send a false application update to a device, whose express purpose is not to successfully corrupt/replace the application software, but instead is the first component of a multi-stage attack in which the initial attack’s objective is to steal the encryption keys from the device. In such a situation, the application is falsely deployed to the device and retrieves the keys. Even though it fails to update, the device uses the telematic capability of the device to offboard the keys and enable a subsequent, more dangerous attack. With such hardware security enabled, you would not be able to read the protected memory locations, the false application update would be rejected, and the device would continue on its way.
A different approach to hardware security is through the utilization of trusted platform modules (TPM). In this case the keys are stored entirely within a different, secure, integrated circuit that is separate from the core product’s processor/memory, and the keys never leave the TPM. Trusted platform modules can also play a role in secure boot as a special sequence initialized only by the correct software, in the correct order, to “unlock” the TPM.
What level of hardware security is appropriate for your application will vary, based on your deployment’s risk profile, the capabilities of your device, and the technologies supported by your server-side infrastructure. What is important is that some consideration is made for securing your device at the hardware level, and that you and your device manufacturing partner are united in your approach to telematic hardware security.
Software Security Onboard a Device
With good hardware security and key storage in place, the updating of the application onboard the device itself can be secured, regardless of whether that update is through firmware updated over the air, or by connecting physically to a device. This security ensures that no bad actor can replace or modify the software onboard your device. This security is achieved by having the application signed with a secret/private key. The signing of this application ensures that the device can verify that the software is genuine, or trusted, before allowing the software to be run on the device.

When transmitting data, there is the protocol being used to transmit data and the method of security that is applied to that protocol. Typically the security and protocol are separate considerations. So whether you are using a popular telematic protocol like MQTT or a UDP IP based protocol like CoAP, there are methods by which that data can be encrypted in its transfer from the device to the Internet, where it then transits to the server. In this sense, most typical security concerns are focused on the data’s pathway through the Internet on its way to its server location more so than the radiation of the data in free space from the device’s antenna.
In the world of data encryption there are two high-level concepts that are important to understand: symmetric encryption and asymmetric communication of data.
Symmetric Encryption
 Symmetric encryption is when you open a “secure channel.” If you think about the President of the United States and the red phone for secure calls, that is a very good analogy for symmetric encryption. This is a secure two-way channel for communication. For applications where the receiver and sender are in the same organization, or the device and end-point receiving the data are designed by the same company, this system is commonly and effectively employed. This technology is commonly used in applications like banking transactions and data at rest (not in transit from one server to another).
Symmetric encryption is when you open a “secure channel.” If you think about the President of the United States and the red phone for secure calls, that is a very good analogy for symmetric encryption. This is a secure two-way channel for communication. For applications where the receiver and sender are in the same organization, or the device and end-point receiving the data are designed by the same company, this system is commonly and effectively employed. This technology is commonly used in applications like banking transactions and data at rest (not in transit from one server to another).
Asymmetric Encryption
In this method of security, there is a public key that can be used to encrypt data to be sent to a receiver, but a secret key that is possessed by the receiver is the only way to decrypt the data. Where different organizations are communicating with one another, or when several organizations might be contributing data to a common dataset, such a security methodology is very effectively used. Asymmetric encryption is commonly used in applications like digital signatures and is a feature of transport layer security (TLS) or secure socket layer (SSL) communications.
One of the shortcomings of asymmetric encryption is that it is much slower to implement and use on devices because the encryption algorithms are complex and require more computational power to run. This is unfortunate for embedded devices where processing capabilities are often a significant limitation. Although symmetric encryption doesn’t require as much computational power, it requires that secret keys be effectively distributed and maintained, which is a separate challenge.
Hybrid Approach
With consideration for the challenges above, it is common in messaging and telematic applications to employ a hybrid model. With this model, an asymmetric message is used to open a secure channel and exchange keys to begin the session between the client and the host, so that session can subsequently be done with safe, secure, lower-overhead symmetric encryption. For example, the client can use a public key to send a message to a host describing all of the information the host needs to connect back to the client using symmetric encryption (a shared secret key).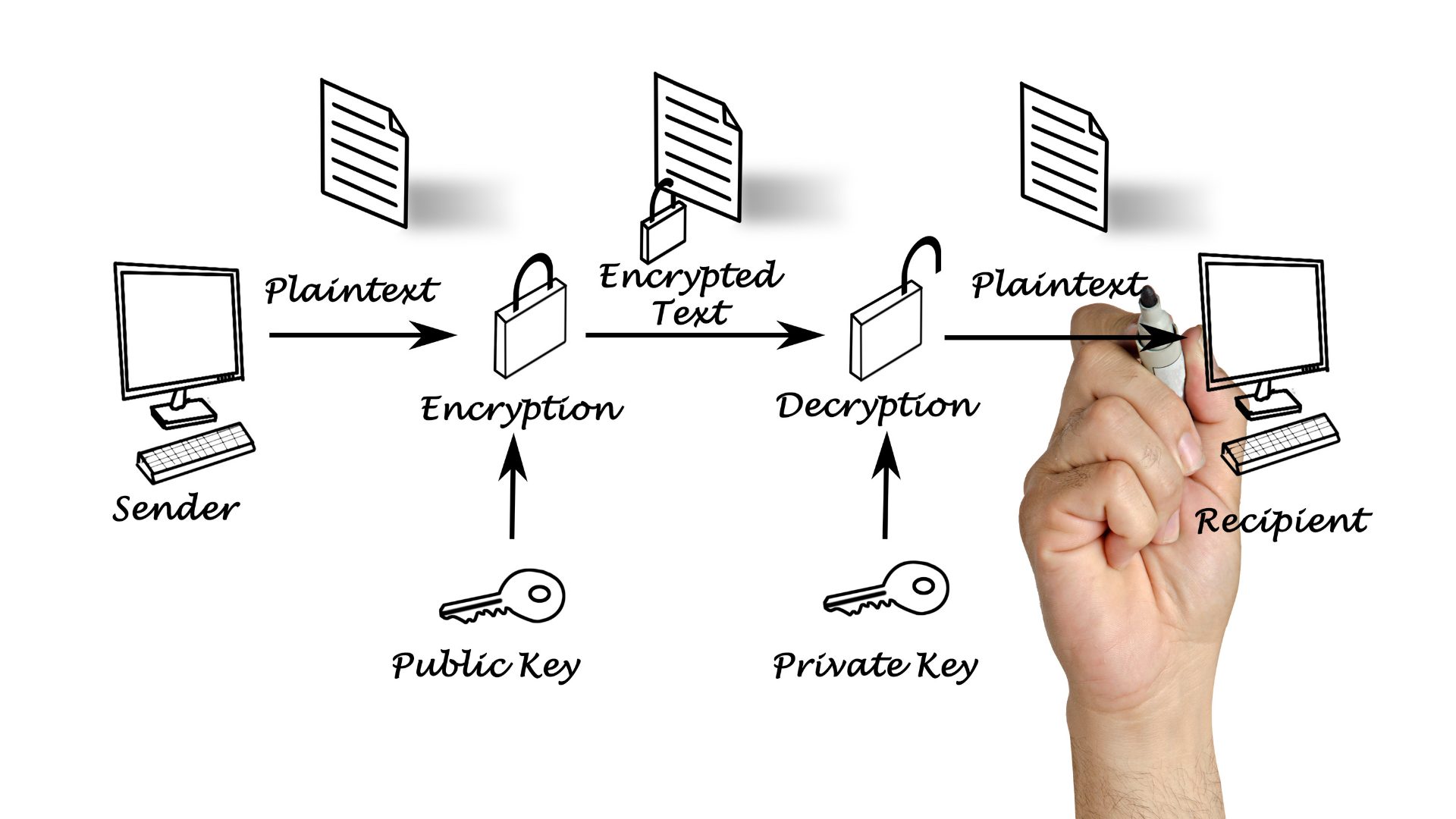
No One-Size-Fits-All Approach
A good security strategy is a collaborative effort between the device manufacturer and the OEM. For example, in a simple asset tracking use case with a battery powered asset tracker that needs to optimize battery life for a longer duration, the asymmetric public key transfer could use 6k of data in the process of sending a one-time 500-byte message. That means that throughout the life of the device, more than 90% of the precious battery life the device is trying to optimize for would be consumed securing the device’s messages. In such cases, like inexpensive IoT sensors feeding asset tracking or environmental intelligence to machinery management systems, the costs in battery life and data transmission may necessitate other approaches to message security.
In a future blog article we’ll cover how a device manufacturer, in collaboration with the cellular or satellite carrier, can be creative in the manner that data is received off the device at the network infrastructure to keep that data off the internet and further contribute to a security solution. Approaches like this can be of considerable assistance when combatting power/data budgets for use cases like the above IoT sensor.
Summary
When considering your connected vehicle deployment, ensure you and your device manufacturer have hardware level key security, signed certificates for software deployment, and a right-sized strategy for encryption of communication to/from the device.
 David Batcheller – President & CBO
David Batcheller – President & CBO
https://www.appareo.com/2020/12/07/top-two-security-issues-for-connected-machines/
8 Benefits of Using Tablets as Displays in Off-Highway and Industrial Machines
The trend is reversing for displays in off-road rugged equipment. Instead of incorporating lots of control logic into display systems, it’s going to become much simpler.
The preeminence of the display as a compute source on the machine, rather than a simple operator interface, was born more of convenience rather than an optimal machine control architecture. When more complex display terminals began to emerge on the market, many of those terminals were utilizing a Windows operating system. The hardware needed to host Windows was left with unutilized computing power. Many organizations, as a result, began taking advantage of that by putting machine control software into the terminal.
Today, however, significant computing potential is possible within embedded devices with a broad spectrum of affordable processor and memory technologies. This gives machinery manufacturers the potential to inexpensively push the control logic out of the terminal and back into the electronic control units, making the displays true thin clients and providing manufacturers much more display flexibility at a lower cost.
Here are 8 ways manufacturers can benefit from using smart devices in place of display terminals.
1. Leverage investments made by consumer electronics manufacturers
Industrial and off-highway vehicle manufacturers and their suppliers are simply not capable of matching pace with the investment and technical progression of the devices in the consumer electronic world. The level of investment and speed of technology deployed in consumer devices by companies like Apple and Samsung is simply not within the reach of industrial and off-highway equipment sectors.
Exacerbating this problem is the limited volumes in the off-highway and industrial spaces — they are only able to access these technologies after they become available in consumer devices, and we then still need to spend years achieving their introduction to a machine. This cycle leaves manufacturers lagging the curve of consumer display expectations by years while investing a lot of time and money into advanced display systems that feel substandard by the time they reach operators (when compared against the latest phone or tablet they carry).
One way of mitigating this problem is by pushing some display functions into mobile devices. Here, without any hardware development or integration investment, equipment manufacturers can leverage the hundreds of millions of R&D dollars put into consumer electronics, as well as the additional investments in the infrastructure that supports them. In this sense, by developing and deploying mobile applications that seamlessly connect with machinery, manufacturers get to leverage the latest in processing and display systems while minimizing investments.

2. Push display features into operator mobile devices
This requires some consideration for both security and safety strategies that vary from manufacturer to manufacturer. On one end of the spectrum, the mobile device can be used as a simple display. The device receives information from the machine over a wireless link. This information is then rendered into value-added real-time information for the operator to view on the phone or tablet display, including whatever visual or auditory alerts are needed by the operator.
On the other end of the spectrum, the mobile device is an interactive element of the machine control architecture. In this embodiment the operator can provide machine control inputs through the phone or tablet — whether that operator is within or outside of the machine’s cab.
And, of course, there are many hybrid models for the utilization of the mobile devices in interaction with off highway and industrial equipment where input capabilities through the mobile device are possible, but limited to a smaller set of functions.

3. Utilize app update infrastructure through Android, Apple, and other devices
Where delivery of a new embedded feature or capability might require a service bulletin, dealer notice, or integration with a new vehicle model year the deployment of complimentary mobile capabilities can be done in a matter of days and launched whenever may be convenient for a vehicle manufacturer.
When coupled with the ability to deliver ECU firmware through the mobile application interface, it becomes possible for vehicle manufacturers to perform significant update campaigns, verify which vehicles have been reached with those campaigns, and to do so without any telematic or dealer service expenses.

4. Break the dependence on vehicle model year release cycles
It has, traditionally, been very difficult to add value for customers of off-highway equipment out of cycle with a machine’s delivery. Should a competitor release a new feature in many circumstances we as an industry are relegated to waiting for the next machine cycle to deliver a competitive response. To the extent that there is mobile experience integrated with the usage of the machine, innovative features enabled through the mobile application can be deployed at any time giving manufacturers the potential to quickly deliver differentiable features out of sequence with machine model year cycles (and make those features available to both new and existing customers).

5. Leverage community to fuel development and growth
With a mobile application also comes the potential to leverage community to fuel development and growth. For example, if there is an industrial segment that is a relatively small consumer of machines but has a strong desire for a specific display, license can be extended by the equipment manufacturer to view and use the data output by the machine. In this manner, a supplier in a specific market segment can develop an application experience that is unique to that one market segment, providing a value added experience to operators in that segment without requiring any development investment, support, or maintenance from the vehicle manufacturer.

6. Rapidly deliver features / speeding to market
Embedded development can be comparatively time consuming and expensive when compared against mobile development. Embedded developers are generally more difficult to hire and train, the software more time consuming to develop and deploy, and the verification and validation activity associated therewith similarly nontrivial. In contrast, working against a defined embedded interface mobile software development is comparatively less expensive, developers more accessible, and software deployment more rapid.
7. Display cost reductions
To the extent that operators are bringing their own devices, and machine displays can become simpler and less expensive, this initiative offers the potential for cost reduction of the machine electrics while delivering more features to its operators.

8. Capture user and machine data
Utilization of a mobile application provides a broad spectrum of possibilities for the capture of both machine and operator data. For machines where telematic connectivity may not be possible, utilization of an application may provide the ability to cache and deliver valuable machine data to a manufacturer (in lieu of the cellular connectivity onboard the machine). The application can also acquire demographics about users, and information about how they navigate and use the application, that can provide user and usage statistics that can become a powerful force for informing future development activity that will help optimize equipment and interfaces for operators.
 David Batcheller – President & CBO
David Batcheller – President & CBO
https://www.appareo.com/2020/11/25/8-benefits-of-using-tablets-as-displays-in-off-highway-and-industrial-machines/

